Preface
I am not sure if the problem lies with configuration in proxmox, or in the OPNsense configuration. I started on this forum because I have a feeling it has to do with virtualization, but mainly because I am not as familiar with it.
The Goal & current configuration
An OPNsense setup on a Proxmox VM with VLANs to a physical switch.
I visualized the setup and switch configuration i use to test VLANs with this image:

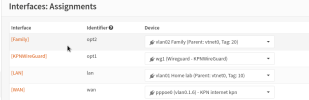
Interface assignments
The firewall on each VLAN interface has an allow any rule. DHCP servers are enabled.
What I understand to be true
1. VLAN aware means that the bridge given to the VM is able to be split into VLANs by the VM. This must be checked on at least the interface used for the Trunk port.
2. The Router Interface with the VLANs must be connected to a Trunk port on the physical switch with the native vlan (PVID?) set to an unused VLAN.
The issue
The VLANs are not functioning as I would expect. The configuration leaves everything unreachable (ping: destination host unreachable).
I feel like I need a sanity check. To my knowledge, the VLAN configuration on the Switch shown in the image should work as intended.
I can only think I am misunderstanding the workings of the Virtualization.
I have heard there is another way of making VLANs, where you would make them on ProxMox and then pass them to the VM so you could configure them as separate interfaces on the VM rather than VLANs. I do not think I prefer this method, I would want VLANs to stay inside the VM for both potential configuration migration to physical systems and the growing amount of VLANs.
Bonus question/issue
I did not make the bridge i use for WAN VLAN aware, but I did successfully create a VLAN on the WAN interface, attached it to a PPPoE network type and get connection from my ISP. Is VLAN aware not required if you only make 1 VLAN?
I do notice the speed is not optimal. I have fiber gigabit, but max speedtest was ~400mbit/s up and down. it's probably a separate issue.
I am not sure if the problem lies with configuration in proxmox, or in the OPNsense configuration. I started on this forum because I have a feeling it has to do with virtualization, but mainly because I am not as familiar with it.
The Goal & current configuration
An OPNsense setup on a Proxmox VM with VLANs to a physical switch.
I visualized the setup and switch configuration i use to test VLANs with this image:

Interface assignments
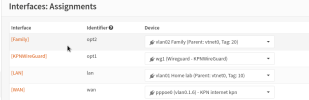
The firewall on each VLAN interface has an allow any rule. DHCP servers are enabled.
What I understand to be true
1. VLAN aware means that the bridge given to the VM is able to be split into VLANs by the VM. This must be checked on at least the interface used for the Trunk port.
2. The Router Interface with the VLANs must be connected to a Trunk port on the physical switch with the native vlan (PVID?) set to an unused VLAN.
The issue
The VLANs are not functioning as I would expect. The configuration leaves everything unreachable (ping: destination host unreachable).
I feel like I need a sanity check. To my knowledge, the VLAN configuration on the Switch shown in the image should work as intended.
I can only think I am misunderstanding the workings of the Virtualization.
I have heard there is another way of making VLANs, where you would make them on ProxMox and then pass them to the VM so you could configure them as separate interfaces on the VM rather than VLANs. I do not think I prefer this method, I would want VLANs to stay inside the VM for both potential configuration migration to physical systems and the growing amount of VLANs.
Bonus question/issue
I did not make the bridge i use for WAN VLAN aware, but I did successfully create a VLAN on the WAN interface, attached it to a PPPoE network type and get connection from my ISP. Is VLAN aware not required if you only make 1 VLAN?
I do notice the speed is not optimal. I have fiber gigabit, but max speedtest was ~400mbit/s up and down. it's probably a separate issue.

