Hello everyone,
first off, i am new to proxmox if i dont know some stuff i am sorry.
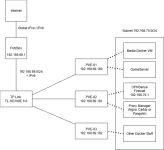
I wanted to build a HomeLab to Learn and have some usable services, heard good stuff about Proxmox. My Hardware consists of 3 old Laptops (HP 2x i7 11. Gen 2x. i7 10 Gen. all 16gb Ram, 1 LAN each) ans a TP Link Switch. My first idea was a cluster between 3 nodes but i cant get that to run and i gave up on that.
Now too my question. Is it possible to achive the drawn network infrastructure (Lines meaning 1 ethernet connection /dotted lines meaning association) in a way that i can connect to my containers form my .69 network to theri .70 addresses?
I tried having a virtual interface with the subnet on each node but that doesnt give me connections between the nodes. Is there an fix / trick to achive this or is this not possible and i need a diffrent solution.
Kind regards
first off, i am new to proxmox if i dont know some stuff i am sorry.
I wanted to build a HomeLab to Learn and have some usable services, heard good stuff about Proxmox. My Hardware consists of 3 old Laptops (HP 2x i7 11. Gen 2x. i7 10 Gen. all 16gb Ram, 1 LAN each) ans a TP Link Switch. My first idea was a cluster between 3 nodes but i cant get that to run and i gave up on that.
Now too my question. Is it possible to achive the drawn network infrastructure (Lines meaning 1 ethernet connection /dotted lines meaning association) in a way that i can connect to my containers form my .69 network to theri .70 addresses?
I tried having a virtual interface with the subnet on each node but that doesnt give me connections between the nodes. Is there an fix / trick to achive this or is this not possible and i need a diffrent solution.
Kind regards