You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
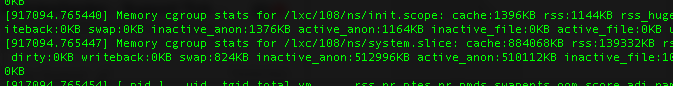
that is not a VM, it is a container - and containers share a kernel (including the kernel's dmesg facility). you can disable access for non-root users (and thus also for unprivileged containers) by setting the sysctl kernel.dmesg_restrict to 1
Yes, I know that.that is not a VM, it is a container
But I think that it is possible like on OpenVZ. Very sad ((
should work - please verify that you set the sysctl correctly (and that you are actually testing with an unpriv. container!)
Code:
$ echo 0 | sudo tee /proc/sys/kernel/dmesg_restrict
0
$ sudo pct enter 123
root@unprivtest:/# dmesg | head -3
[ 0.000000] Initializing cgroup subsys cpuset
[ 0.000000] Initializing cgroup subsys cpu
[ 0.000000] Initializing cgroup subsys cpuacct
root@unprivtest:/# exit
$ echo 1 | sudo tee /proc/sys/kernel/dmesg_restrict
1
$ sudo pct enter 123
root@unprivtest:/# dmesg | head -3
dmesg: read kernel buffer failed: Operation not permitted
root@unprivtest:/# exit