Hello there,
I am trying to passthrough my motherboard onboard audio to a Windows 10 guest, but every time it boots it crashes on blue screen;
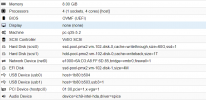
the lspci --nnk output for the audio card I want to passthrough is
while the graphic card is
grub options are set as follow
As far as I can understand each device has its own IOMMU group (12 for the audio card, 22 for the GPU and 23 for the audio device integrated in the GPU), cause from
relevant line output are
and checking the respective folders are the only device in there
Before trying this I successfully passed through the host video card to the guest, following the indication on both the manual and the wiki;
trying to passthrough the audio card I added to /etc/modprobe.d/blacklist.conf the last line (the previous 3 are for the GPU passthrough)
I also added the second line to /etc/modprobe.d/vfio.conf (again, previous one for the GPU)
and updated initramfs, then i edited
/etc/pve/qemu-server.201.conf (201 is my VM device ID) adding
hostpci1: 00:1b.0
(while hostpci0: 03:00.0;03:00.1,pcie=1,romfile=GTX10606Gb.rom is the line for the GPU passthrough)
Without the hostpci1 line the VM boots fine, as long as I try to configure the audio card adding that line I get blue screen on boot.
I also tried installing Windows from scratch, it boots fine as long as the GPU drivers are not loaded, but as soon as I try to load gpu drivers it crashes with blue screen, in both cases with
am I missing something? Is there something else I should add? How can I circumvent the problem?
Thank you in advance
Roberto
I am trying to passthrough my motherboard onboard audio to a Windows 10 guest, but every time it boots it crashes on blue screen;
the lspci --nnk output for the audio card I want to passthrough is
Code:
00:1b.0 Audio device [0403]: Intel Corporation 82801JI (ICH10 Family) HD Audio Controller [8086:3a3e]
Subsystem: Intel Corporation 82801JI (ICH10 Family) HD Audio Controller [8086:0041]
Kernel driver in use: vfio-pci
Kernel modules: snd_hda_intelwhile the graphic card is
Code:
03:00.0 VGA compatible controller [0300]: NVIDIA Corporation GP106 [GeForce GTX 1060 6GB] [10de:1c03] (rev a1)
Subsystem: Micro-Star International Co., Ltd. [MSI] GP106 [GeForce GTX 1060 6GB] [1462:3283]
Kernel driver in use: vfio-pci
Kernel modules: nvidiafb, nouveau
03:00.1 Audio device [0403]: NVIDIA Corporation GP106 High Definition Audio Controller [10de:10f1] (rev a1)
Subsystem: Micro-Star International Co., Ltd. [MSI] GP106 High Definition Audio Controller [1462:3283]
Kernel driver in use: vfio-pci
Kernel modules: snd_hda_intelgrub options are set as follow
Code:
GRUB_CMDLINE_LINUX_DEFAULT="quiet intel_iommu=on pcie_acs_override=downstream,multifunction video=efifb:off"As far as I can understand each device has its own IOMMU group (12 for the audio card, 22 for the GPU and 23 for the audio device integrated in the GPU), cause from
Code:
find /sys/kernel/iommu_groups/ -type l
Code:
/sys/kernel/iommu_groups/12/devices/0000:00:1b.0
/sys/kernel/iommu_groups/22/devices/0000:03:00.0
/sys/kernel/iommu_groups/23/devices/0000:03:00.1and checking the respective folders are the only device in there
Before trying this I successfully passed through the host video card to the guest, following the indication on both the manual and the wiki;
trying to passthrough the audio card I added to /etc/modprobe.d/blacklist.conf the last line (the previous 3 are for the GPU passthrough)
Code:
blacklist radeon
blacklist nouveau
blacklist nvidia
blacklist snd_hda_intelI also added the second line to /etc/modprobe.d/vfio.conf (again, previous one for the GPU)
Code:
options vfio-pci ids=10de:1c03,10de:10f1 disable_vga=1
options vfio-pci ids=8086:3a3eand updated initramfs, then i edited
/etc/pve/qemu-server.201.conf (201 is my VM device ID) adding
hostpci1: 00:1b.0
(while hostpci0: 03:00.0;03:00.1,pcie=1,romfile=GTX10606Gb.rom is the line for the GPU passthrough)
Without the hostpci1 line the VM boots fine, as long as I try to configure the audio card adding that line I get blue screen on boot.
I also tried installing Windows from scratch, it boots fine as long as the GPU drivers are not loaded, but as soon as I try to load gpu drivers it crashes with blue screen, in both cases with
Code:
Stopcode: SYSTEM SERVICE EXCEPTION or SYSTEM THREAD EXCEPTION NOT HANDLED
What failed: nvlddmkm.sysam I missing something? Is there something else I should add? How can I circumvent the problem?
Thank you in advance
Roberto
Last edited: