Hi,
im trying to create a new VLAN interface for my VMs
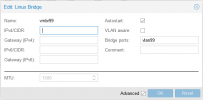
Im not using a VLAN aware bridge, I want to create a dedicated VLAN interface that I select when adding a NIC to the VM, pretty much like VMWare.
When i create the Linux VLAN, presumably its better to assign it to the NIC rather than the vmbr? which i have done and i can see it in the list of interfaces.
However on the VM it doesnt appear as an interface to choose, am i missing something?
Im running v 6.4-8
thanks!
Ian
im trying to create a new VLAN interface for my VMs
Im not using a VLAN aware bridge, I want to create a dedicated VLAN interface that I select when adding a NIC to the VM, pretty much like VMWare.
When i create the Linux VLAN, presumably its better to assign it to the NIC rather than the vmbr? which i have done and i can see it in the list of interfaces.
However on the VM it doesnt appear as an interface to choose, am i missing something?
Im running v 6.4-8
thanks!
Ian