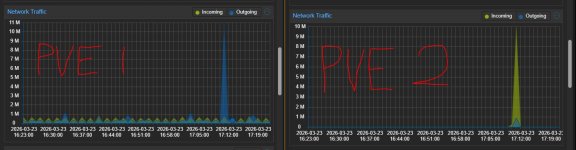
Something is running on one of my PVE nodes every hour, 11 minutes past the hour. I can see data going out from PVE 1 going to PVE 2 but I have no cronjobs set up for that time.
PVE 2 was about to be decommissioned so everything's now shut down on it and that's how I noticed this little spike in traffic every hour.
I checked all the cronjobs in every LXC on PVE 1 and nothing is scheduled.
No cronjobs on either of the hosts.
I checked journalctl as well but nothing shows up there either.
I'm stumped.
PVE 2 was about to be decommissioned so everything's now shut down on it and that's how I noticed this little spike in traffic every hour.
I checked all the cronjobs in every LXC on PVE 1 and nothing is scheduled.
No cronjobs on either of the hosts.
I checked journalctl as well but nothing shows up there either.
I'm stumped.