hello
i have an easy setup. 3 active networks and it seems it works flawless.
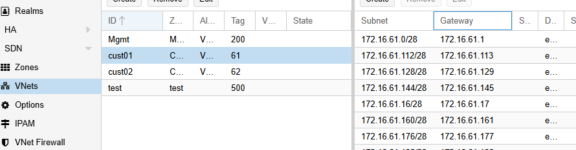
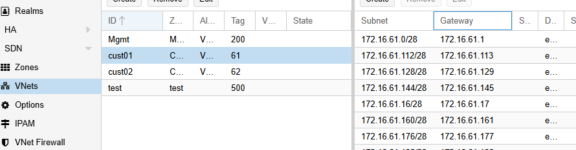
i have the issue with sdn, vnets. i created in the vnet my 16 subnets, /28er
but the VMs cant ping the gateways, like 1, or 17 and so on.
is there any trick ?
the vm just ad the NIC in the hardware tab "cust01". but how the VM itself knows in which network it belongs ? as i read proxmox does know it on its own. from the right config. for example: VM IP 172.16.61.2, with the gateway 172.16.61.1 and proxmox knows its belongs to the first subnet.
the VM cant ping the 1 gateway (also non other vm), no active firewalls on proxmox or vm. as i read with ip show bridgename i should see the gateways 172.16.6.1.1,17,33 and so on but i dont see any of it.
one important point: we havent yet a working dns. my last believe its because of the missing dns server " or the missing ipam !
any idea ? any tricks ?
regards
i have an easy setup. 3 active networks and it seems it works flawless.
i have the issue with sdn, vnets. i created in the vnet my 16 subnets, /28er
but the VMs cant ping the gateways, like 1, or 17 and so on.
is there any trick ?
the vm just ad the NIC in the hardware tab "cust01". but how the VM itself knows in which network it belongs ? as i read proxmox does know it on its own. from the right config. for example: VM IP 172.16.61.2, with the gateway 172.16.61.1 and proxmox knows its belongs to the first subnet.
the VM cant ping the 1 gateway (also non other vm), no active firewalls on proxmox or vm. as i read with ip show bridgename i should see the gateways 172.16.6.1.1,17,33 and so on but i dont see any of it.
one important point: we havent yet a working dns. my last believe its because of the missing dns server " or the missing ipam !
any idea ? any tricks ?
regards

