
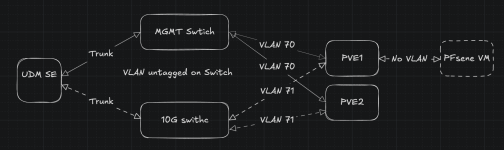
I have my home lab running at my friends.currently I have an bridge internal to pve that I have connected to pfsense and define vlans in pfsense.
it works but I wanna move more into automation and this isn't pfsense strong side.
hence I wanna switch to proxmox SDN, but I want all my vnets to be routable in pfsense
I do not understand how to solve this and Ai gives me confusing answers.
I would like to not mess with my friends network internal to my lab.
so I want to not have vlan conflicts with his network
as far I as I understand I need a VXlan and OSPF fabric to enable this?
but I dont understand how I get PFsense to see my vnets?
do I need a BGP controller and BGP in pfsense to enable this?
if like for routing between pfsense and my SND vnets to be automatic.
I cant find any good guides or videos, tho im not sure what im looking for as SDN and BGP is way over my head.
I hope someone here can give me pointers?
EDIT: I added a simple drawing of my current network config.
Last edited:

