I am unable to boot from the new kernel 6.17.13-7. Any help finding a workaround is greatly appreciated.
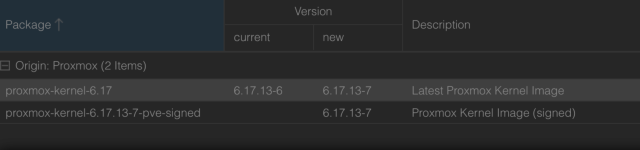
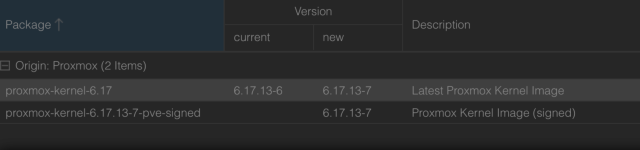
I have performed the kernel update to fix the DirtyFrag vulnerability, and there is a ZFS incompatibility with the new kernel. This instance was running 6.17.13-6 and the only updates that were performed were:
proxmox-kernel-6.17: 6.17.13-6 -> 6.17.13-7
After the update, boot was unable to finish due to a ZFS feature not supported:
com.truenas:block_cloning_endian (Fixes BRT ZAP endianness on new pools.)
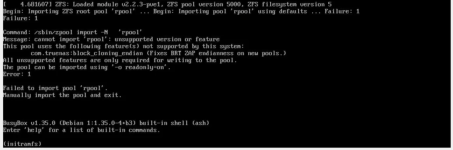
I am able to boot fine by choosing 6.17.13-6 at GRUB. Looking at the settings, I see the following:
I am not able to set it to disabled, however:
I have performed the kernel update to fix the DirtyFrag vulnerability, and there is a ZFS incompatibility with the new kernel. This instance was running 6.17.13-6 and the only updates that were performed were:
proxmox-kernel-6.17: 6.17.13-6 -> 6.17.13-7
After the update, boot was unable to finish due to a ZFS feature not supported:
com.truenas:block_cloning_endian (Fixes BRT ZAP endianness on new pools.)
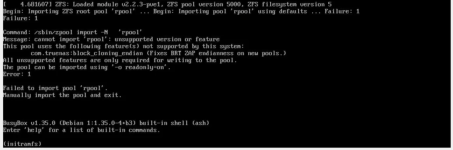
I am able to boot fine by choosing 6.17.13-6 at GRUB. Looking at the settings, I see the following:
Bash:
# zpool get com.truenas:block_cloning_endian rpool
NAME PROPERTY VALUE SOURCE
rpool com.truenas:block_cloning_endian - default
Bash:
# zpool get all rpool | grep block_cloning_endian
rpool feature@block_cloning_endian active localI am not able to set it to disabled, however:
Code:
# zpool set feature@block_cloning=disabled rpool
cannot set property for 'rpool': property 'feature@block_cloning' can only be set to 'disabled' at creation time
